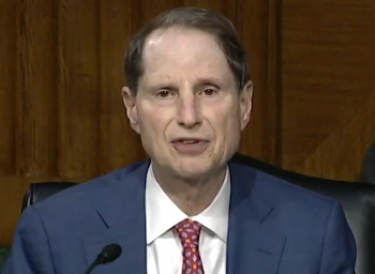
Reuters reported that Ron Wyden, a Democrat member of the Senate Intelligence Committee, could provide additional insight on the downsides of broken encryption before a hearing was held on the government's legislation.
Juniper had included code from the NSA in its NetScreen security software which created a means of eavesdropping through its equipment and this had been altered, either by internal or external sources, providing access to traffic from users.
Researchers exposed the change in the Dual Elliptic Curve, a security mechanism that was widely believed to contain a backdoor.
|
|
“Congress and the American people must understand the serious national security risks associated with weakening the encryption that protects Americans’ personal data, as well as government and corporate systems.”
The EARN IT Act aims to add riders to the use of section 230 of the Communications Decency Act that allows online platforms to escape liability for things their users say and do.
For example, one can sue the person who defamed you on a platform like Twitter, but not the platform itself. An amendment to this section in 2018 has made platforms liable for publishing information designed to facilitate sex trafficking.
The new bill makes it necessary for platforms to earn the immunity that Section 230 has afforded so far. And one of the conditions for earning that immunity could well be the ditching of end-to-end encryption.
Wyden and Republican Mike Lee of the Judiciary Committee have written to Juniper chief executive Rami Rahim, asking what happened to an investigation that the company had said it was conducting after the unauthorised code was found.
The battle for a backdoor into encrypted platforms has been going on since 2016, when the FBI demanded that Apple create a new version of its iOS operating system so that the agency could guess the passcode on an iPhone 5 that was owned by a terrorist.
The case went to court, Apple refused and finally the FBI paid a commercial firm to get the data.
In a more recent case, the FBI asked Apple for help in unlocking an iPhone used by a man who shot dead three people in Florida. In this case, too, the FBI managed to gain access on its own.
The UK passed legislation in 2016 that would permit the breaking of encryption and Australia followed suit in 2018.