In a post on Thursday, company founder Eugene Kaspersky said the attack used an invisible iMessage with a malicious attachment. A number of vulnerabilities in iOS were used to install malware.
"The deployment of the spyware is completely hidden and requires no action from the user," he wrote.
"Further, the spyware also quietly transmits private information to remote servers: microphone recordings, photos from instant messengers, geolocation and data about a number of other activities of the owner of the infected device."
|
|
"It was found that several thousand telephone sets of this brand were infected," FSB said in a statement [Google translation thanks to Ars Technica].
"At the same time, in addition to domestic subscribers, facts of infection of foreign numbers and subscribers using SIM cards registered with diplomatic missions and embassies in Russia, including the countries of the NATO bloc and the post-Soviet space, as well as Israel, SAR and China, were revealed.
"Thus, the information received by the Russian intelligence services testifies to the close cooperation of the American company Apple with the national intelligence community, in particular the US NSA, and confirms that the declared policy of ensuring the confidentiality of personal data of users of Apple devices is not true."
Kaspersky [the firm] has been on the NSA's radar ever since it exposed hacks of various entities by Western agencies. It began with the Russian firm exposing the UK's GCHQ in 2014, which tried to hack a Belgian telecommunications provider.
In 2015, Kaspersky exposed an entity it called the Equation Group, which has been long rumoured to be an internal NSA unit. The company also detailed how the Stuxnet operation was carried out to cripple Iran's nuclear reactors. Stuxnet was discovered by Sergey Ulasen in 2010; he joined Kaspersky Lab a year later. The virus was infiltrated into Iran's nuclear labs through an USB drive as the lab was not connected to any external network.
Israeli Government hackers breached the Kaspersky network in 2014; after the company found out in 2015, it wrote a detailed analysis of the incident.
Kaspersky employee Igor Kuznetsov detailed the method of the Triangulation infection. He outlined the process of infection as given under:
- "The target iOS device receives a message via the iMessage service, with an attachment containing an exploit;
- "Without any user interaction, the message triggers a vulnerability that leads to code execution;
- "The code within the exploit downloads several subsequent stages from the C&C server, that include additional exploits for privilege escalation;
- "After successful exploitation, a final payload is downloaded from the C&C server, that is a fully-featured APT platform; and
- "The initial message and the exploit in the attachment is deleted."
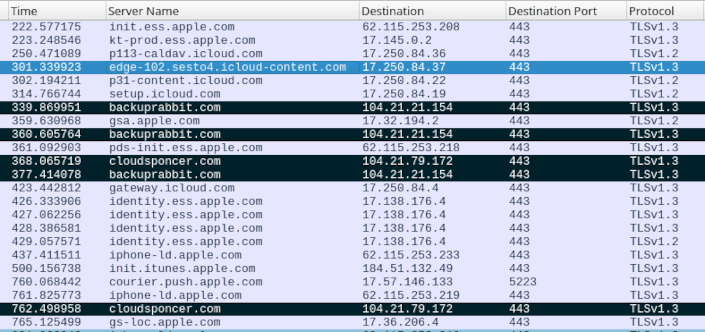
Kuznetsov also posted a Wireshark screenshot [below] of connections to multiple C&C domains.
Kaspersky was hit with a ban on the use of its products in the US public sector in 2018, after US mainstream media had published a series of stories claiming it was leaking data to Russian intelligence services, something the company strongly denied.
Since then, the firm has cut back operations in the US and set up so-called transparency centres where companies can sign up to look at the source code of its products.
In his post, Eugene said he was sure that his company was not the main target of the attacks.
"We believe that the main reason for this incident is the proprietary nature of iOS. This operating system is a 'black box' in which spyware like Triangulation can hide for years," he said.
"Detecting and analysing such threats is made more difficult by Apple’s monopoly of research tools, making it the perfect haven for spyware. In other words, as I have said more than once, users are given the illusion of security associated with the complete opacity of the system.
"What actually happens in iOS is unknown to cyber-security experts. The absence of news about the attacks does not at all indicate the impossibility of the attacks themselves – as we have just seen."












































