Microsoft claimed the attackers had been identified as Midnight Blizzard aka Nobelium, the same group that attacked security firm FireEye in 2020 using a supply chain through the Orion network monitoring product sold by SolarWinds.
This is the second occasion in recent times that foreign actors have spent long periods within Microsoft's corporate networks without being detected.
In July last year, an intrusion into Microsoft's Azure cloud led to the breaching of email accounts belonging to American envoy to Beijing, Nicholas Burns, assistant secretary of state for East Asia, Daniel Kritenbrink and also US Commerce Secretary Gina Raimondo among others.
|
|
In November, Microsoft released a blog post claiming the company had put in place what it called a Secure Future Initiative which it described as a "new initiative to pursue our next generation of cybersecurity protection."
In Friday's blog post, Microsoft said the attacker had used password-spraying — or random guesses — to compromise what it called "a legacy non-production test tenant account" and then used this access to enter "a very small percentage of Microsoft corporate email accounts".
There was no explanation as to how a non-production test account provided a path to corporate email accounts.
Microsoft's statement also made it plain that two-factor authentication, now an article of faith to protect email accounts, was not being used for these corporate accounts.
The company said that the corporate email accounts accessed by the attacked included "members of our senior leadership team and employees in our cyber security, legal, and other functions".
The attackers "exfiltrated some emails and attached documents. The investigation indicates they were initially targeting email accounts for information related to Midnight Blizzard itself. We are in the process of notifying employees whose email was accessed".
The company claimed the incident had "highlighted the urgent need to move even faster. We will act immediately to apply our current security standards to Microsoft-owned legacy systems and internal business processes, even when these changes might cause disruption to existing business processes.
"This will likely cause some level of disruption while we adapt to this new reality, but this is a necessary step, and only the first of several we will be taking to embrace this philosophy.
"We are continuing our investigation and will take additional actions based on the outcomes of this investigation and will continue working with law enforcement and appropriate regulators.
"We are deeply committed to sharing more information and our learnings, so that the community can benefit from both our experience and observations about the threat actor. We will provide additional details as appropriate."
Former Facebook chief security officer Alex Stamos said on social media: "Microsoft just announced that they were breached by the SVR, the same Russian intelligence agency that broke into SolarWinds.
"This is a big deal, and Microsoft owes all of us a much more detailed description of what happened."
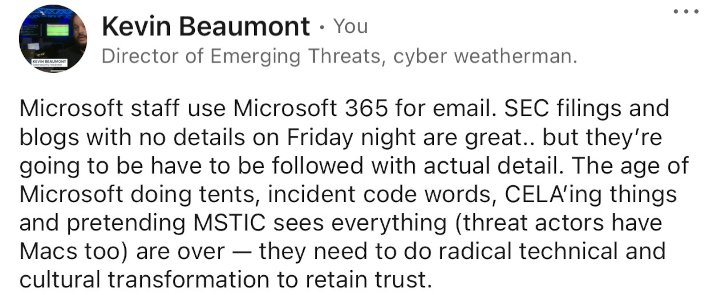
Ace British security researcher Kevin Beaumont agreed with this. "I agree with @alex here, Microsoft needs to do a much more public disclosure," he wrote. Microsoft staff use Microsoft 365 email with Exchange Online. Eg I was gossi @ microsoft.com.
"I think MS needs to explain to M365 customers how mailboxes were accessed via password spraying."











































