The exploit was demonstrated on Sunday in a talk titled "what the Fax?" at the DEFCON security summit held in Las Vegas. A detailed technical explanation of the methods used is available here.
Researchers Eyal Itkin and Yaniv Balmas said though there was an impression that fax was an ancient technology, it was widely used today with more than 300 million fax numbers in use.
"By our estimates, there are currently hundreds of millions of fax machines still in use around the world. Financial reports from Wall Street indicate that tens of millions of all-in-one printers are sold worldwide each year," they said.
|
|
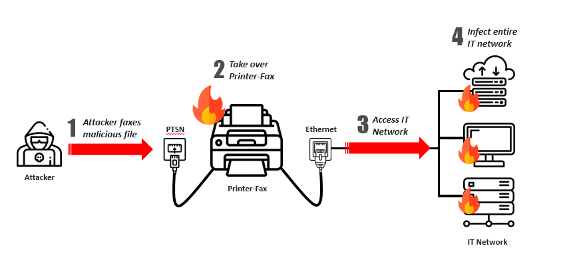
The duo said they had found critical vulnerabilities in widely used implementations of the fax protocol.
"These vulnerabilities allow an attacker with mere access to a phone line, and a fax number to attack its victim’s all-in-one printer – allowing him full control over the all-in-one printer and possibly the entire network it's connected to," the researchers said.
The leaked NSA exploits Eternal Blue and Double Pulsar were used by Itkin and Balmas to gain access to other Windows computers on the network to which the printer was attached.
They were then able to do whatever they wanted on the PC, and demonstrated how they sent back a file from the victim's PC to the fax machine that they were using.
"Once an all-in-one printer has been compromised, anything is possible. It could be used to infiltrate the internal network, steal printed documents, mine bitcoin, or practically anything," Itkin and Balmas said.
They said they had worked closely with HP to patch the vulnerabilities and patched firmware had been published by the company on 1 August.
Commenting on the research, Ray Rothrock, chairman and chief executive of security firm RedSeal, said: “By 2025, 75 billion devices will be linked to the Internet. While this connectedness exponentially improves productivity, as Check Point’s news confirms, vulnerabilities with staggering implications already exist within every network.
"Activated by phone lines versus the Internet, at least one billion new threat sources are inside our defences and it’s only a matter of time before they’re called to action. Yes, threat prevention and ensuring all devices’ software are up-to-date help. However that is not enough. To mitigate this very real risk, every company must accept that it’s only a matter of time before these lurking threats are activated. They must focus on resilience.
"In response to this news, we recommend companies validate their segmentation policies and make sure there’s very limited access to their most valuable assets. This isn’t a one-and-done exercise. Companies must remain vigilant, constantly monitoring all possible pathways within and between their network environments so they can quickly isolate a compromised device. As Check Point’s news shows, we can’t predict new, exploitable vulnerabilities. However, we can — and we must — be resilient.”
Graphic: courtesy Check Point









































