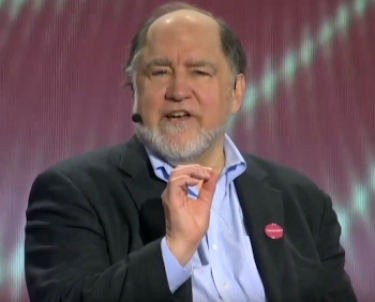
Rivest, a professor at the Massachusetts Institute of Technology and the R in the famous RSA public-key cryptosystem, was responding to a question from RSA chief technology office Zulfikar Ramzan who was moderating the Cryptographers' Panel, an annual feature at the RSA Security Conference, held in San Francisco this week
"Blockchain is the wrong security technology for voting. I like to think of it as bringing a combination lock to a kitchen fire or something like that..," he said. "It's good on its own for certain things but it's not good for voting."
With the US in election mode as the primaries are in progress with an election due in November, the question about using technology to make the process more secure has been discussed often, especially in view of the hysteria around alleged foreign interference in the polls.
|
|
"Blockchain technology really doesn't fit for a couple of reasons... one is that we have learned we need software independence. For many things we do in society, like flying an airplane, you need hi tech.
"Voting is an activity where you actually don't need hi-tech to make it work. You can get by just fine with paper ballots if you can keep that as your foundation.
"And if you do use some technology, use the paper ballots to check on it and you can do very well. We call this software independence, so you don't need to trust the results because you trust some software. That's a dangerous path to go down if you don't need to go down that path and with voting we really don't need to."
Rivest said blockchains provided certain things and had the audience laughing when he added, "I like to think of it as garbage in, garbage stored for ever. Once they've had the chance to manipulate your vote, it goes on the blockchain and never gets changed again."
He once again emphasised it was not the right technology for voting. "And so I think blockchains are a mismatch for voting. Blockchains may have other wonderful places to apply... but voting's not one of those."
The other panellists were Adi Shamir, the A in RSA and Borman Professor of Computer Science at the Weizmann Institute in Israel; Whitfield Diffie, cryptographer and security expert at Cryptomathic; Tal Rabin, head of Research at the Algorand Foundation; and Arvind Narayanan, Associate Professor of Computer Science at Princeton University.